The 2026 NASCIO-Deloitte Cybersecurity Study reads like a post-mortem for the digital status quo. Only 26 percent of state chief information security officers feel they can fend off AI-enabled threats. This signals a crisis of confidence in an era of automated aggression. While bureaucrats in state capitals debate the merits of incrementalism, the digital gates are being torn down by automated swarms.
We saw this panic before during a 2025 ransomware wave that hit a small county clerk’s office. It was a humid 90-degree Tuesday with 2 inches of rain pooling on the asphalt outside, but the atmosphere in the office was freezing. The city manager stared at a frozen terminal while a ransom clock ticked down: the silence in that server room was absolute. That silence is what RYT aims to disrupt.
The Architecture of Cellular Defense
The industry is pivoting. States are researching a “whole-of-state” approach to unify fragmented services onto a single resilient ledger. This represents a total philosophical shift. Critics worry that a unified ledger creates a larger target, but the vanguards at RYT argue that siloes are actually the greatest liability. The current model is an exercise in distributed neglect.
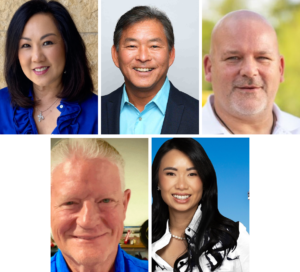
“Maintaining hundreds of separate databases means paying for separate security, compliance, auditing, and infrastructure for each one,” said Jeff Mahony, Chief Architect at RYT. “Most are individually underfunded, which is why breaches keep happening. A shared RYT ledger or subnet consolidates those costs. One security model is funded properly instead of hundreds funded poorly. The result is a lower total cost and stronger security. RYT’s great tech, but it’s not magic, the simple truth is concentrated investment outperforms distributed neglect.”
Winning the Velocity War
Europol’s 2026 IOCTA report warns of a “Velocity Gap” where automated criminal exploits outpace the slower pulse of sovereign infrastructure. In this landscape, hesitation is a death sentence. To win, the ledger must move faster than the bureaucrat.
“Criminals use AI to exploit vulnerabilities in milliseconds. Human-led bureaucracies respond in months. RYT closes that gap by automating the response at the ledger level,” Mahony notes. “But it’s not a traditional ‘detect and block’ approach where the attacker knows they’ve been caught and adapts. PoM’s behavioral enforcement silently identifies malicious actors and excludes them from consensus. They continue attacking without knowing their actions have zero impact on the network. They waste resources on a dead end while the network operates normally. No human bureaucracy needed.”
This “ghosting” of attackers is a tactical masterstroke. The malicious actors continue their work without realizing their actions have zero impact on the network. They waste resources on a digital dead end while the network operates normally.
The Civic Check and Balance
Trust in a whole-of-state model requires more than just code: it requires a coalition. RYT diversifies its network to ensure the ledger remains impartial, creating a technical version of the “separation of powers.”
“PoM’s validator topology is a technical implementation of the separation of powers,” Mahony says. “Validators are drawn from state agencies, public universities, civic institutions, and judicial bodies. No single category has enough validators to reach consensus on its own. A compromised government node can’t push through a fraudulent state change because consensus requires participation across all categories. The architecture makes unilateral action structurally impossible as every category of participant is necessary, none is sufficient on its own.”
The Fiscal ROI of Survival
With 16 percent of state CISOs reporting budget cuts in 2026, the financial barrier to innovation is significant. However, maintaining calcified, poorly defended legacy databases is a sinkhole that states can no longer afford. The math is simple; efficiency is a security feature.
The whole-of-state pivot is a nascent term in the 2026 policy cycle. For the three quarters of CISOs currently staring down an AI-driven crisis, it is the only architecture robust enough to offer a way out. This is not about incremental tech upgrades; it is about the ROI of survival in an age of mercenary code.